“What? Huh? Why?”
Those are some of the many questions I was asking myself. Simply… Looking to challenge the brain in different ways than what I’m normally doing.
How it began – In my personal time while trying to secure my own personal hosted infrastructure, I was noticing that there wasn’t an efficient or effective way to block bad threat actors (nasty hackers) on the Internet.
The typical (tedious) approach has always been:
- I see a bad connection from IP1, therefore I must block IP1.
- I see a bad connection from IP2, therefore I must block IP2.
- I see a bad connection from IP3, therefore I must block IP3.
- ….
- Repeat until you lose all sense of sanity.
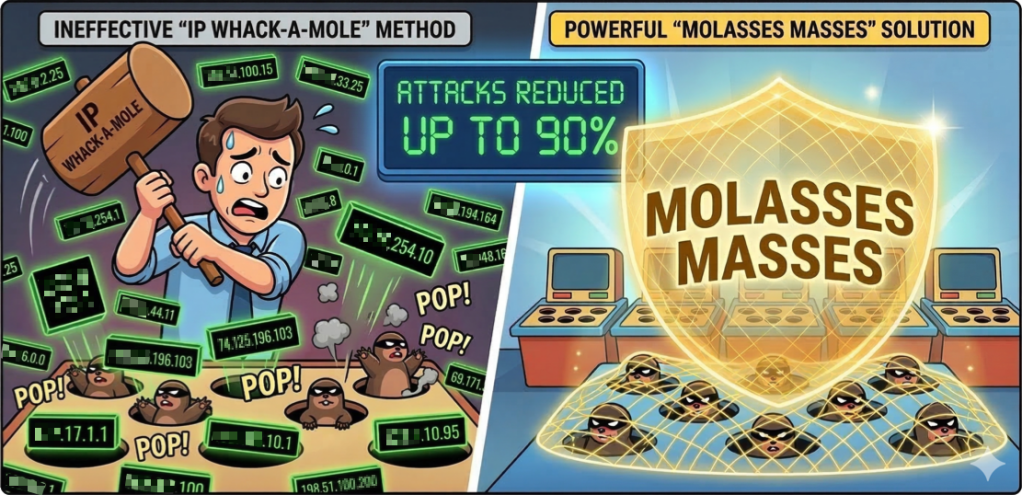
The problem with this approach is that you end up getting stuck in a game of whack-a-mole. Who do you think wins? Trick question – it’s not you!
I put a different idea together – what if bad threat actors run their hacking world like a business and focus on cost optimization and automation. Novel idea right?
How does this apply to what I do? Well if I were to run a business like theirs, I would figure out how to “copy/paste” my attacks in creative ways. To do this, I would choose a (cheap) hosting provider that has resources that I can use for my desired purposes. Once the hosting provider is identified, I’m going to figure out ways to spin up new resources in a quick manner in a different location (i.e. automation).
New Resource + New Location = New IP Address To Attack From
Now that I know this, let the hacking begin!
Do you see how the game of whack-a-mole starts?
What does my company do?
I have a few products available now, but the one product that solves the above problem is a product called Molasses Masses.
How does it work?
Rather than blocking on a per-IP basis, I get all the subnets for that hosting provider that the hacker is using and then block those. The idea is that remote connections coming to my/your hosted services, should not come from other hosting providers. It should be from people like you reading this article!
Now it’s possible that you or your business partners get caught up in the block list – no problem! You can exclude your own and/or business partner subnets from the specifically curated list of subnets that you download.
How effective it this?
I’ve seen a reduction of attacks of up to 90%* from all my honeypots on the Internet.
Why would you use this?
Got remote users that need to VPN into your organization?
Got hosted services that should be accessed from actual users, and not random bots sitting in hosted environments?
Then this is the product for you!
Integrations available?
Very simply, It’s a flat text file of curated subnets that you can use in your own policies..
These are the supported platforms available today to consume my product:
- Linux (shorewall)
- Cisco – Firepower Threat Defense (FTD)
- Fortinet – Fortigate Firewalls
- Palo Alto Networks – PAN-OS and Prisma Access.
Curious to test it out? 7-day free trials available.
Use discount code MM2026 to snag a 20% discount on checkout for the first 50 customers 🙂